Blog

Best Luxurious Men’s Perfume 2026: Top Picks and Guide
Hey, hunting for a luxurious men’s perfume in 2026 that lasts all day and actually gets you compliments? These are ...

High Tech Homes: Merging Decoration with 2026 Tech
The divide between technology and interior design has officially closed. The cluttered era of exposed wires and obtrusive devices is ...
Fixing Page Fault in Nonpaged Area: Easy Ways to Stop That Scary Blue Screen
Imagine this: You’re in the middle of a game or just browsing, and bam your screen turns blue with words ...

Will Your Next Doctor Be an Algorithm? AI in 2026 Medicine
The question is no longer speculative. In 2026, the answer is not a simple “yes” or “no” but a transformative ...
Agentic AI Pindrop Anonybit Fraud Defense
Discover how agentic AI Pindrop Anonybit combats deepfake fraud with privacy-focused biometrics stats, strategies, and 2026 trends for secure AI ...

How the Internet is Transforming Education in the Digital Age
The internet has fundamentally reshaped education, making learning more accessible, dynamic, and personalized than ever before. By providing instant access ...

Hallux Valgus: An Orthopedic Approach to Biomechanical Correction
While commonly perceived as a painful bump on the big toe, Hallux Valgus-the medical term for a bunion-is recognized by ...
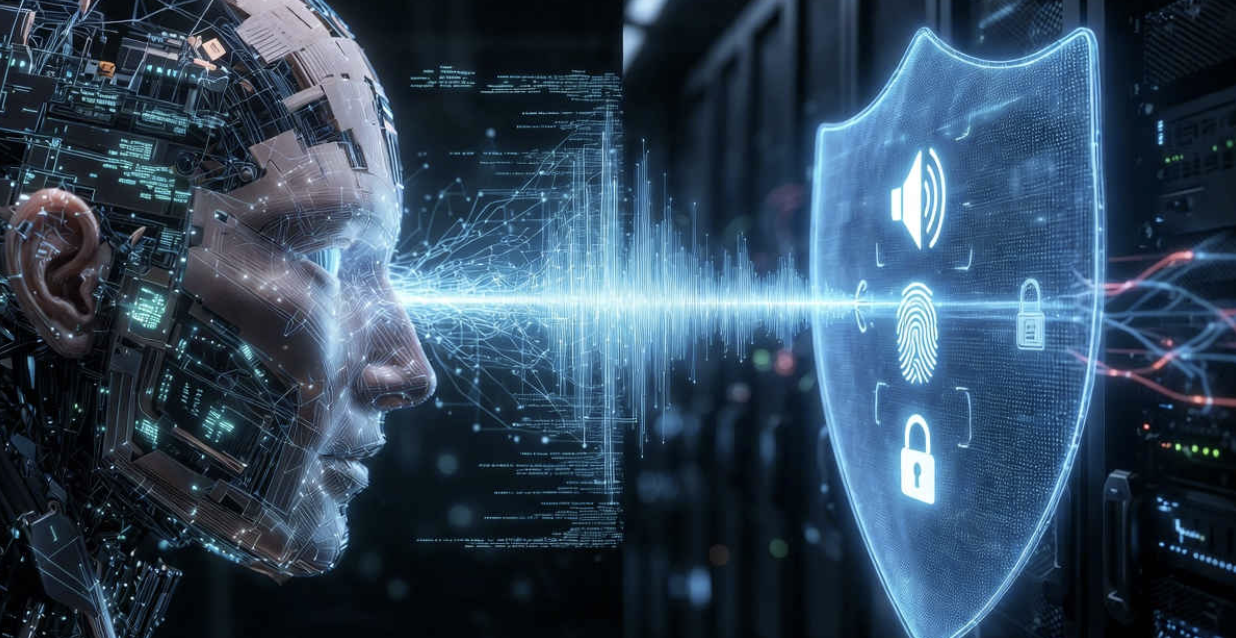
Fixing Your Windows PC with DISM Online Cleanup Image RestoreHealth: A Friendly Guide
Have you ever felt like your computer is throwing a tantrum? It slows down, crashes, or refuses to update, and ...

Master FMCDealer: Login, Tools & Fixes
Unlock Ford’s FMCDealer portal secrets: Easy login guides, outage fixes, and pro tips for dealers. Stay ahead in 2026. Key ...

The Dawn of Agentic AI: When Chatbots Start Doing the Work
For the past few years, AI interactions have largely centered around conversation. Tools like ChatGPT, Claude, and other large language ...